What is BlackRuby2 ransomware? And how does it carry out its attack?
BlackRuby2 ransomware is a new version of the notorious BlackRuby ransomware. It is a new iteration of the Infinite Tear ransomware group. just like its previous version, this crypto-malware is designed to target and encrypt user-generated files in infected PCs. According to researchers, this new variant seems to be better and even more dangerous compared to its predecessor.
Since BlackRuby2 ransomware is a new strain of the Infinite Tear malware group, its behavior adheres to a generic algorithm. According to the reports made by security experts, this ransomware opens out a couple of delivery mechanism. Before it starts to carry out its attack, BlackRuby2 ransomware performs several checks in the infected PC such as:
- Regional Settings Check – this is done to determine the user’s country and preferences.
- Security Software Check – this is done to scan the local system for any kind of security software installed in the computer.
- System Profile Information – this is done to get information related to the PC’s installed software as well as hardware components.
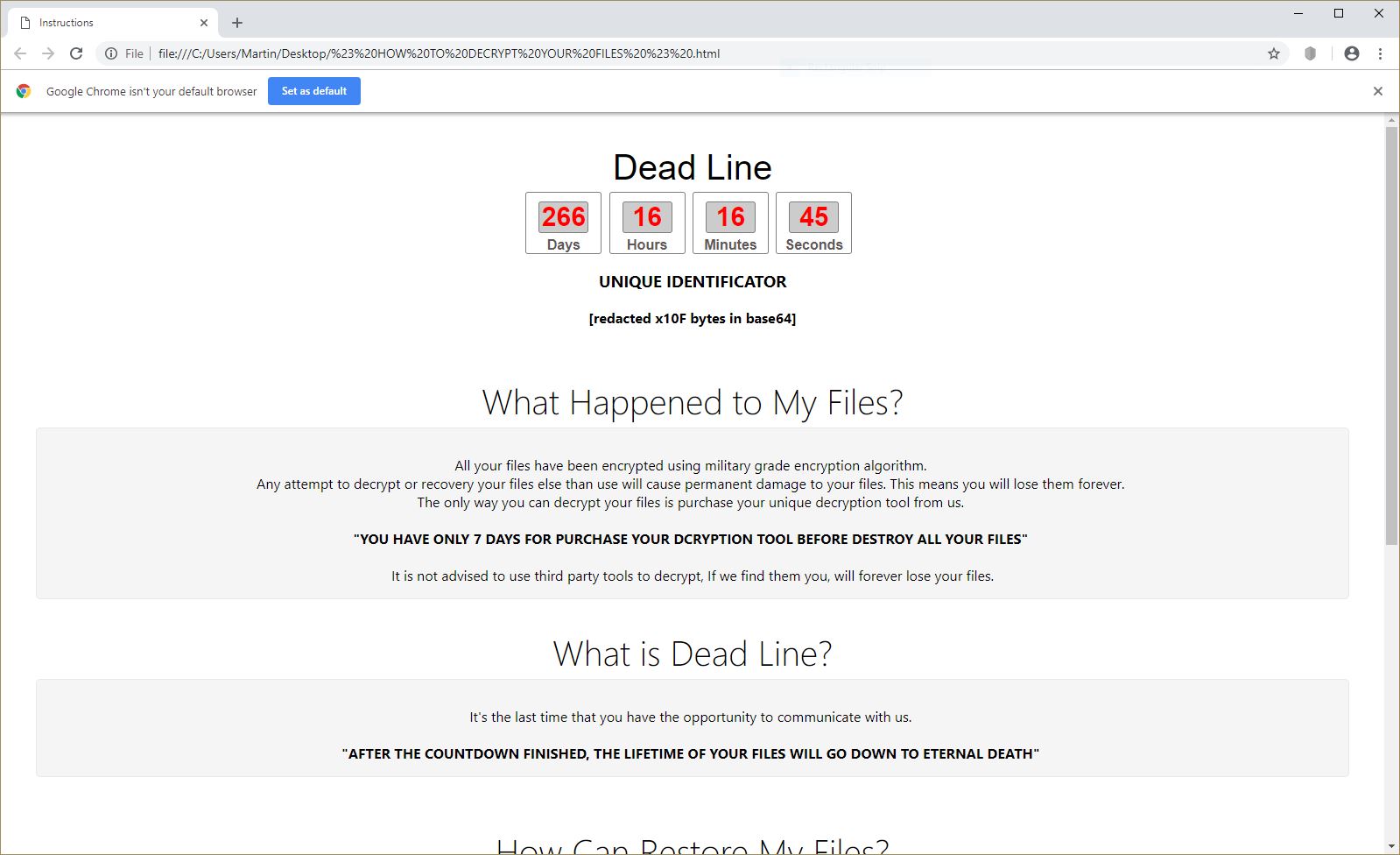
After it completes its checklist, BlackRuby2 ransomware will begin its encryption process using a sophisticated encryption algorithm and append the .BlackRuby2 extension on the affected files. Similar to its previous version, this new variant targets files that are mostly user-generated such as images, documents, videos, audio files, database and so on. It then opens up a file named “HOW-TO-DECRYPT-FILES.txt which contains a very long ransom note that states:
“BlackRuby2
===================== Identification Key =====================
–
===================== Identification Key =====================
[Can not access your files?]
Congratulations, you are now part of our family #BlackRuby Ransomware. The range of this family is wider and bigger every day.
Our hosts welcome our presence because we will give them a scant souvenir from the heart of Earth.
This time, we are guest with a new souvenir called “Black Ruby”. A ruby in black, different, beautiful, and brilliant, which has been
bothered to extract those years and you must also endure this hard work to keep it. If you do not have the patience of
this difficulty or you hate some of this precious stone, we are willing to receive the price years of mining
and finding rubies for your relief and other people of the world who are guests of the black ruby.
So let’s talk a little bit with you without a metaphor and literary terms to understand the importance of the subject.
It does not matter if you’re a small business or you manage a large organization, no matter whether you are a regular
the user or a committed employee, it’s important that you have a black ruby and to get rid of it, you need to get back to the previous situation and we need the next step.
The breadth of this family is not supposed to stop because we have enough knowledge and you also trust our knowledge.
We are always your backers and guardian of your information at this multi-day banquet and be sure that no one in the world can take it from you except for us who extracts this precious stone.
We need a two-sided cooperation in developing cybersecurity knowledge. The background to this cooperation is a mutual trust, which will result in peace and tranquility. you must pay us worth of Bitcoins to restore your system to the previous state and you are free to choose to stay in this situation or return to the normal.”
If your computer ended up getting infected with BlackRuby2 ransomware, remember that paying the ransom won’t really give you the solution you’re looking for. In fact, most of the ransomware victims are ignored by cyber crooks once they receive the payment. At the time of writing, a free decryptor hasn’t been released yet so for the meantime, make use of any backup copies of your affected files.
How does BlackRuby2 ransomware spread its malicious payload?
In a similar way, BlackRuby2 ransomware also uses spam emails in spreading its malicos payload just like its previous version. Developers of ransomware threats often attach a corrupted file in spam emails. Such files may be documents with macro scripts used to download and install BlackRuby2 ransomware on the targeted device.
Obliterating BlackRuby2 ransomware isn’t easy so you have to follow the guidelines given below.
Step 1: Open the Task Manager by simply tapping Ctrl + Shift + Esc keys on your keyboard.
Step 2: Under the Task Manager, go to the Processes tab and look for any suspicious-looking process which takes up most of your CPU’s resources and is most likely related to BlackRuby2 ransomware.

Step 3: After that, close the Task Manager.
Step 4: Tap Win + R, type in appwiz.cpl and click OK or tap Enter to open Control Panel’s list of installed programs.
Step 5: Under the list of installed programs, look for BlackRuby2 ransomware or anything similar and then uninstall it.

Step 6: Next, close Control Panel and tap Win + E keys to launch File Explorer.
Step 7: Navigate to the following locations below and look for BlackRuby2 ransomware’s malicious components such as [random file name].doc or [random file name].exe and key.txt as well as other suspicious files and then delete all of them.
- %TEMP%
- %WINDIR%\System32\Tasks
- %APPDATA%\Microsoft\Windows\Templates\
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 8: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use Advanced System Repair Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 9: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 10: Navigate to the following paths:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 11: Delete the registry keys and sub-keys created by BlackRuby2 ransomware.
Step 12: Close the Registry Editor and empty the contents of Recycle Bin.
It is important to make sure that nothing is left behind and that BlackRuby2 ransomware is completely removed use the following antivirus program. To use it, refer to the instructions below.
Perform a full system scan using Advanced System Repair Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, http://advancedsystemrepair.com/ASR_Installation.exein the Run dialog box and then tap Enter or click OK.
- After that, it will download Advanced System Repair Pro. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run Advanced System Repair Pro to perform a full system scan.
- After the scan is completed click the “Fix, Clean & Optimize Now”button.