What is Vault ransomware? And how does it execute its attack?
Vault ransomware is a new file-encrypting malware designed to lock important files in a computer. It is a typical crypto-malware that seems to target Russian-speaking users. And just like a typical ransomware threat, once it infects a computer, it drops several malicious that help it in executing its attack.
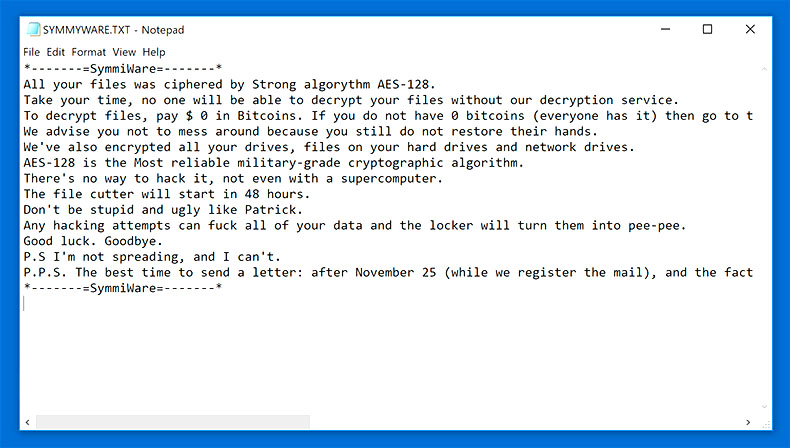
After it drops its malicious files, it also makes modifications in the Windows Registry which allows it to run on every system boot. It then begins the encryption process by using a strong encryption algorithm which security experts believe to be either AES or RSA ciphers. Following data encryption, it adds the .vault suffix on every affected file and releases its ransom note stating:
“&————————————————————————————————————————
MAIN QUESTIONS
————————————————————————————————————————–
Accessing your files has been temporarily suspended.
The analogy between your files and a glass vase. At the moment, “vase” (= your data) is divided into a million small pieces (encrypted). The reverse process (Recovery) can be made only with your private key, which is stored securely on our servers. To restore files, you need to fill up your personal account (specified on the main page, under Payment)
————————————————————————————————————————–
After replenishing your purse in the transaction list will be visible to your replenishment when the cost will be repaid in full – you will automatically be issued a key and all the necessary software to recover. Alas, you cannot restore all the information in the original form without your unique klyucha.Ni system administrators or programmers, or even anti-virus companies will not be able to help you. Keep in mind that your files are encrypted using a cryptographically unique RSA key. For getting detailed technical information, please visit: Wikipedia (RSA) – this is your case.
————————————————————————————————————————–
You are in a fully automated system with which you can get all that you need for recovery.
- After the first time, you are logged in using VAULT.KEY, our life creates a personal page for you. All information on your personal the page is stored in our database and is available for you at any time.
- Use the resource you get a recovery guarantees. You can visit fayov decrypt and recover multiple files for free that would be confident in the possibility of recovery. Note that some important files (such as XLS) can pass through our testing, for obvious reasons, for free restore valuable files like you can not. If you do not believe in the recovery is a particular file – ask us to send a screenshot of the file.
- You can write to us using the Message page.
- Partial file recovery payment, our system will automatically take money from you and will count them on your balance. If full payment key system automatically generates for you the software needed to fully restore the file (more details about the recovery process – below).
————————————————————————————————————————–”
How does Vault ransomware spread online?
Vault ransomware spreads via malicious spam email campaigns. This isn’t new as cyber crooks tend to use spam emails to spread their malware creations like Vault ransomware. This is why you have to careful in opening emails and their attached file for it might be a malicious payload of ransomware threats like Vault ransomware.
To kill this crypto-malware from your computer, refer to the instructions given below.
Step 1: Close the program window of Vault ransomware. If you find it hard to do so, tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step 2: Go to Processes and look for the malicious process of Vault ransomware like Vault.exe and other suspicious processes then right click on each one of them and select End Process or End Task to kill their processes.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for dubious programs that might be related to Vault ransomware and then Uninstall it/them.

Step 5: Tap Win + E to launch File Explorer.
Step 6: After opening File Explorer, navigate to the following directories below and look for Vault ransomware’s malicious components and remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry before you proceed to the next steps below. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by Vault ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by Vault ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty the contents of Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Vault ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Right after you followed the removal guide above complete the removal process of Vault ransomware using [product-name].
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Tpe in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.
- After the scan is completed click the “Fix, Clean & Optimize Now”button.