What is 3301 Ransomware?
The 3301 Ransomware is an encryption ransomware Trojan that is primiarily designed and used to take over the victims’ computers and demand the payment of a ransom. Unexceptionally like most encryption ransomware Trojans, this 3301 Ransomware will encrypt the contents of the users’ drives, making the user’s data inaccessible and unreadable. The 3301 Ransomware will then demand a ransom from the user in exchange for the decryption key that is required to recover the encrypted files. Security researchers strongly advise computer users to take extra precautions against this such 3301 Ransomware and numerous other threatening encryption ransomware Trojans that are currently active.
The 3301 Ransomware could be related to the Karmen Ransomware, an RaaS or simply Ransomware as a Service platform mainly used to create customized ransomware Trojans. So, basically this 3301 Ransomware is a customized version of this encryption Trojan RaaS, and it is also unknown who is behind the attack. The 3301 Ransomware is spread through the use of spam email messages. Mainly, the victims will receive an email message tempting them to open an attached Microsoft Word file, which includes corrupted macro scripts that download and install the 3301 Ransomware onto the victim’s computer right after it is opened So always check the sources and don’t simply open spam emails to be most sure. In the recent years, this has become the preferred way of distributing encryption ransomware Trojans and other mlaware like the 3301 Ransomware. Because through this, learning how to handle email attachments safely, having an effective anti-spam method, and disabling macros and scripts in Microsoft Word and other software unless absolutely necessary, are all very essential steps to take and consider to prevent ransomware Trojan infections such as the 3301 Ransomware.
3301 Ransomware Ransom Demand
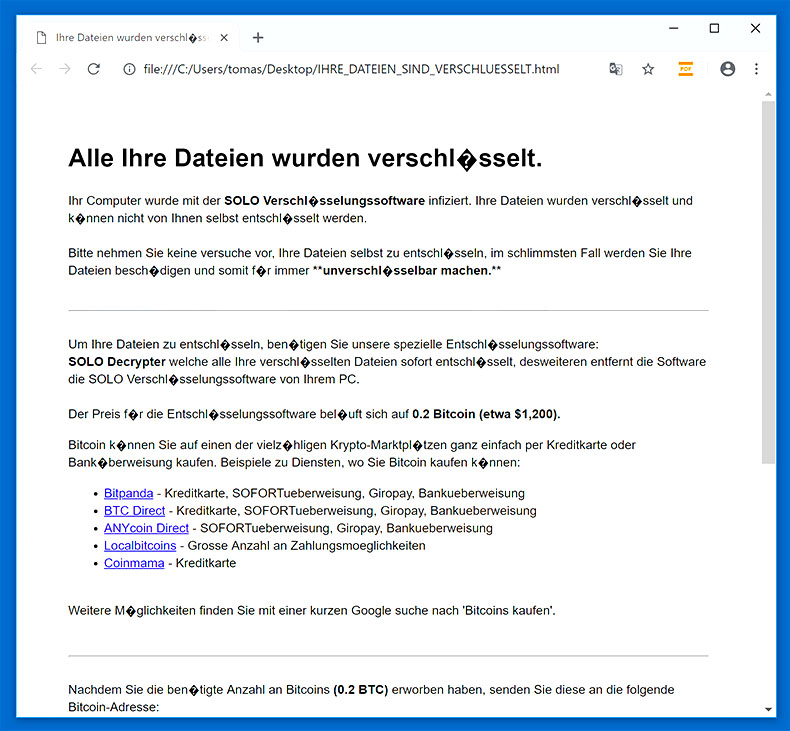
Once the files and other data of the victim are encrypted, the 3301 Ransomware will deliver its ransom note. To do this, the 3301 Ransomware will show its ransom message in a pop-up window on the screen, as well as modify the infected computer’s desktop wallpaper image. Below is the following is the full text of the 3301 Ransomware ransom note:
‘Ransomware 3301
! Attention !
All your documents, photos, databases
and other important files have been encrypted.
Only way to decrypt your files is to receive the private key and decryption program To receive the private key and decryption program go to any crypted folder inside there is the special file (DECRYPT_MY_FILES.HTML) with complete instructions how to decrypt your files.’
Primarily, the 3301 Ransomware will target commonly used file types associated with popular software such as Microsoft Office of MySQL. The 3301 Ransomware wil also target the victim’s photos, audio, and video files. The 3301 Ransomware will then rename the affected files by appending the file extension ‘.3301’ to each affected file’s name. The 3301 Ransomware ransom note is delivered in the form of an HTML file that is shown on the infected computer’s desktop. This HTML file, named ‘DECRYPT_MY_FILES.HTML’ and contains the text above, which is also advising computer users to connect to a website on the Dark Web using the TOR browser and paying a certain ransom of 0.00036 BTC to download the decryptor necessary to restore the affected files.
How to deal with a 3301 Ransomware Infection?
It is also very essential that computer users should not accept and be paying the ransom the 3301 Ransomware demands in its ransom note. Because there is no guarantee that the extortionists will respond and keep their promise after the victim pays up to $1000 USD for the decryptor. Or if they do, the decryptor delivered may not work, the con artists may ask for more money or ignore the victim altogether instead. Moreover, the victim may be targeted for additional infections and paying these ransoms allows con artists to continue developing threats like the 3301 Ransomware just to feed their fantasy and generate more money. Instead, computer security analysts highly advise computer users to take steps to protect their data from threats like the 3301 Ransomware by investing into a an effective backup system and a reliable anti-malware application that is fully up-to-date. Most especially, the backups are the best protection against malware and ransomware Trojans like the 3301 Ransomware since they allow the recovery of the affected files without making any ransom payment.
Security Doesn’t Let You Download SpyRemover Pro or Access the Internet?
Solutions: Your computer may have malware hiding in the memory that doesn’t allow any program, including SpyRemover Pro, from executing on your computer. Follow to download SpyRemover Pro and gain access to the Internet:
- Try to use an alternative browser. Malware may disable your default browser. If you’re using IE, for instance, and having problems downloading SpyRemover Pro, try to open Firefox, Chrome or Safari browser instead.
- Try to use a removable media. Download SpyRemover Pro on another clean computer, then burn it to a USB flash drive, DVD/CD, or any preferred removable media, then simply install it on your infected computer and run SpyRemover Pro’s malware scanner.
- Try to start Windows in Safe Mode. If you can not access your Window’s desktop, kindly reboot your computer in “Safe Mode with Networking” and then simply install SpyRemover Pro in Safe Mode.
How to eliminate 3301 Ransomware Manually?
- Press Ctrl+Alt+Delete.
- Go to the Task Manager.
- Kill suspicious randomly named processes that could belong to the malware by clicking the End Task button.
- Leave Task Manager and tap Windows Key+E.
- Check your Desktop, Temporary Files, and Downloads folders.
- Look for malicious recently downloaded files that may have got the system infected.
- Right-click these files and press Delete.
- Find the %APPDATA% folder.
- Look for a suspicious file named iekaewe.exe or similarly, right-click it and select Delete.
- Close the File Explorer.
- Empty the Recycle bin.
- Reboot the system.
How to automatically remove 3301 Ransomware?
Basic steps of SpyRemover Pro:
Step 1. Run SpyRemover Pro installer
Click on the .exe file that just downloaded in the lower right corner of your browser window.
Step 2. Click Yes
Click Yes to accept the User Account Control settings dialog.
Step 3. Foll0w setup instructions
Follow the instructions to get SpyRemover Pro set up on your computer and you will be good to go!
“use a one click solution like SpyRemover Pro”