What is Docx ransomware? And how does it implement its attack?
Docx ransomware is a new file-encrypting threat that was found to be using the same distribution IP addresses as GandCrab ransomware. It was discovered by a malaware security researcher named “S!Ri” and is designed to encrypt stored data in a computer leaving it inaccessible to victims.
The instant it infects a system, it drops a malicious file which contains the following parameters:
SHA256:30ec73110c97a5ac5e923324b6874c41777a31b9b8a95467babcb9fb6bd3e982
Name:25d7ebac.gxe
Afterwards, Docx ransomware makes changes in some critical Windows settings and system files such as:
- advapi32.dll
- comctl32.dll
- gdi32.dll
- kernel32.dll
- oleaut32.dll
- user32.dll
- version.dll
The files listed above are modified in order to perform a lot of unauthorized procedure calls and actions. After that, it proceeds to employ data gathering module used to gather information about the user and the system. The information obtained is used for another module called stealth protection used to keep any security programs and antivirus programs from interrupting the attack. The crypto-malware then proceeds to scan the computer for files with the following extensions:
.PNG .PSD .PSPIMAGE .TGA .THM .TIF .TIFF .YUV .AI .EPS .PS .SVG .INDD .PCT .PDF .XLR .XLS .XLSX .ACCDB .DB .DBF .MDB .PDB .SQL .APK .APP .BAT .CGI .COM .EXE .GADGET .JAR .PIF .WSF .DEM .GAM .NES .ROM .SAV CAD Files .DWG .DXF GIS Files .GPX .KML .KMZ .ASP .ASPX .CER .CFM .CSR .CSS .HTM .HTML .JS .JSP .PHP .RSS .XHTML. DOC .DOCX .LOG .MSG .ODT .PAGES .RTF .TEX .TXT .WPD .WPS .CSV .DAT .GED .KEY .KEYCHAIN .PPS .PPT .PPTX .INI .PRF Encoded Files .HQX .MIM .UUE .7Z .CBR .DEB .GZ .PKG .RAR .RPM .SITX .TAR.GZ .ZIP .ZIPX .BIN .CUE .DMG .ISO .MDF .TOAST .VCD SDF .TAR .TAX2014 .TAX2015 .VCF .XML Audio Files .AIF .IFF .M3U .M4A .MID .MP3 .MPA .WAV .WMA Video Files .3G2 .3GP .ASF .AVI .FLV .M4V .MOV .MP4 .MPG .RM .SRT .SWF .VOB .WMV 3D .3DM .3DS .MAX .OBJ R.BMP .DDS .GIF .JPG .CRX .PLUGIN .FNT .FON .OTF .TTF .CAB .CPL .CUR .DESKTHEMEPACK .DLL .DMP .DRV .ICNS .ICO .LNK .SYS .CFG
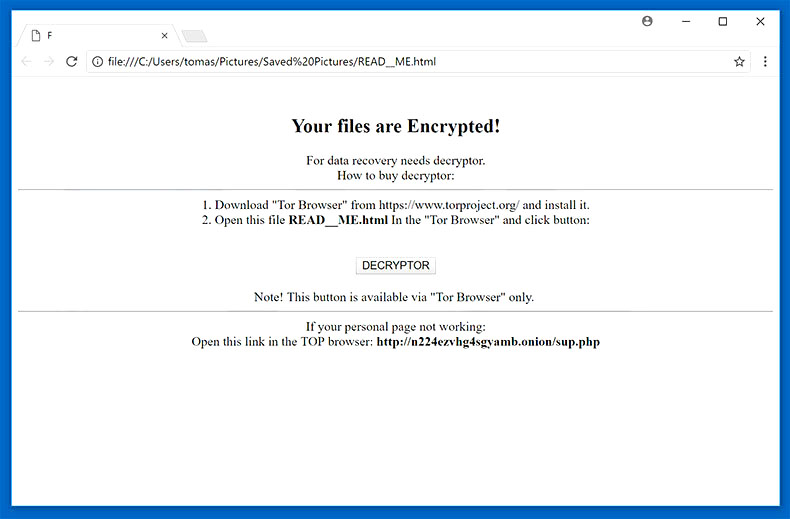
Once it finds its targeted files, Docx ransomware encrypts them using a sophisticated encryption algorithm and releases a file named “YOU_FILES_HERE.txt” that contains the following message:
“Your files are Encrypted!
For data recovery needs decryptor.
How to buy decryptor.
- Download “Tor Borwser” from https://torproject.org/and install it.
- Open this link In the “Tor Browser”
{TOR URL HERE}
Note! This link is available via “Tor Browser” only.
If Tor/Tor browser is locked in your country or you can not install it, open one of the following links:
{ALTERNATIVE URLS}
Free decryption as guarantee.
Before paying you can send us 2 file for free decryption.
You unique ID: {ID}”
How does Docx ransomware spread online?
Docx ransomware may spread via malicious spam email campaigns. Crooks tend to attach malicious payload in emails and send them to users using spam botnets. They may be disguised as receipts, bank statements, invoices and other seemingly legitimate emails to trick users into opening them.
Make sure to use the removal guide below as a reference to terminate Docx ransomware from your computer.
Step 1: Open the Task Manager by tapping Ctrl + Shift + Esc keys.
Step 2: Go to the Processes tab and look for the malicious processes of Docx ransomware and then right click on it and select End Process or End Task.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step 4: Look for dubious programs that might be related to Docx ransomware and then Uninstall it/them.
Step 5: Close Control Panel and then tap Win + E to launch File Explorer.

Step 6: After opening File Explorer, navigate to the following directories below and look for Docx ransomware’s malicious components such as YOU_FILES_HERE.txt, [random].exe and other suspicious-looking files and then erase them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by Docx ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by Docx ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Docx ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Once you’re done executing the steps given above, you need to continue the removal process of Docx ransomware using a reliable program like [product-name]. How? Follow the advanced removal steps below.
- Turn on your computer. If it’s already on, you have to reboot it.
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.

- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.

- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.

- After the scan is completed click the “Fix, Clean & Optimize Now” button.












