What is Veracrypt ransomware? And how does it implement its attack?

Veracrypt ransomware is a file-encrypting malware that belongs to the Aurora ransomware group. Like other Aurora variants, this one is designed to corrupt data, leaving them inaccessible to victims. It uses a “.veracrypt” suffix in marking its encrypted files. It also seems to be targeting Russian-speaking users since its ransom note is written in the Russian language. At the time of writing, it isn’t known yet if the group or individual who created Aurora ransomware are the same ones who created Veracrypt ransomware.
The moment its payload is dropped in the system, it creates new malicious files that are needed for the next phase of the attack. Some of these malicious files take control of essential system processes so that Veracrypt ransomware can remain undetected until it has finished its attack. Moreover, it also exploits the auto-execute system functionality by setting some malicious values in the Run and RunOnce registry sub-keys. Once this happens, it achieves persistence on the infected device.
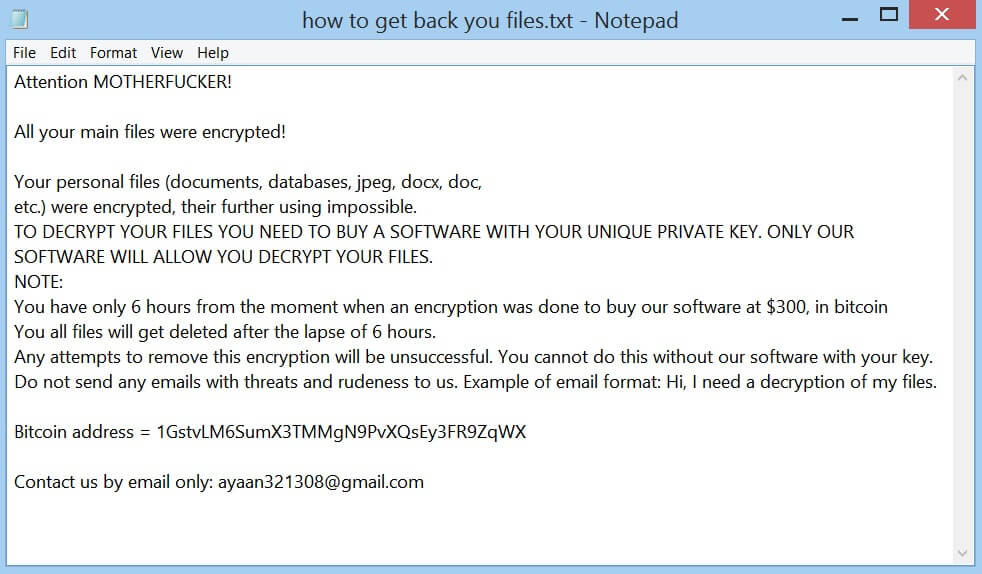
After the alterations are made, Veracrypt ransomware scans the system to look for files to encrypt. Typical ransomware threats like this one usually target user-generated files like documents, videos, images, audio and many more. Once it finds these files, it encrypts them and adds the .veracrypt extension to each one of the encrypted files. It then drops three text files namely, “@@_ATTENTION_@@.txt”, “@@_README_@@.txt” and “@@_README_@@.txt” which contains the same content that states:
“$$$$$$$$$$$$$$$$$> CRYPTO LOCKER <$$$$$$$$$$$$$$$$
Ваши файлы были зашифрованы уникальным ключем.
Расшифровка без этого ключа невозможна в принципе.
Настоятельно рекомендуем не пытаться самостоятельно их расшифровать.
В случае повреждения файлов мы не сможем расшифровать их в дальнейшем.
Рекомендуем вам не обращаться в компании по восстановлению данных.
Они просто свяжутся с нами, купят ключ и продадут его вам по более высокой цене.
Если вы хотите расшифровать свои файлы, вам нужно получить у нас RSA-ключ.
Чтобы получить ключ RSA, выполните следующие действия по порядку:
Оплатите выкуп на BTC-кошелек: >>> 19byE1fxToZXcmfXixFZmRy9E9i1QFYmLv <<<
1. $200 долларов в первые 24 часа, $400 долларов по истечению 24 часов
2. Напишите на [email protected], [email protected], [email protected]
+ укажите ссылки на BTC-транзакцию в сообщении.
===========
!ВНИМАНИЕ!
Прикрепите файл 000000000.key из %appdata% к сообщению электронной почты,
без этого мы не сможем расшифровать ваши файлы.
===========
Только мы можем успешно расшифровать ваши файлы.
В ответном письме вы получите уникальный дешифратор и инструкции о том, что делать дальше.
Мы гарантируем вам восстановление файлов, если вы все правильно сделаете.
$$$$$$$$$$$$$$$$$> CRYPTO LOCKER <$$$$$$$$$$$$$$$$”
How does Veracrypt ransomware spread online?
Just like its predecessors, Veracrypt ransomware might spread online via malicious spam email campaigns where an obfuscated file is attached. This file may be a ZIP file, PDF file, or a document with macro scripts used to launch Veracrypt ransomware on the computer. This is why you have to be careful in opening any emails no matter who the sender is as it could contain the malicious payload of Veracrypt ransomware.
Obliterate Veracrypt ransomware from your computer with the help of the removal instructions laid out below.
Step_1: First, boot your computer into Safe Mode with Networking, and afterward, you have to terminate the malicious processes of Veracrypt ransomware using the Task Manager and to open it, tap Ctrl + Shift + Esc keys.
Step_2: Go to the Processes tab and look for the malicious processes of Veracrypt ransomware and then right-click on it and select End Process or End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to Veracrypt ransomware and then Uninstall it/them.
Step_5: Close Control Panel and then tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below:
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: From these directories, look for the malicious components of Veracrypt ransomware such as “@@_ATTENTION_@@.txt”, “@@_README_@@.txt” and “@@_README_@@.txt”, as well as “[random].exe” and then delete all of them
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step_8: Close the File Explorer and tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by Veracrypt ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_10: Delete the registry keys and sub-keys created by Veracrypt ransomware.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if Veracrypt ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
On the other hand, you can also check out a free decrypter from Emsisoft that might help in restoring the files encrypted by Veracrypt ransomware.
Congratulations, you have just removed Veracrypt Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove Veracrypt Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
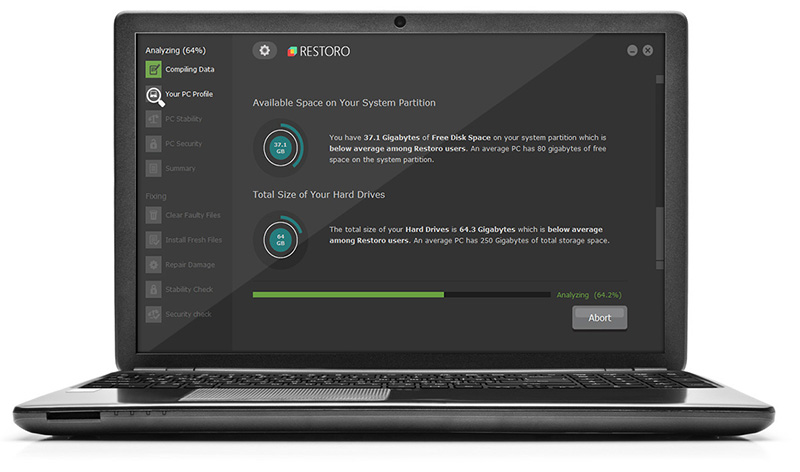
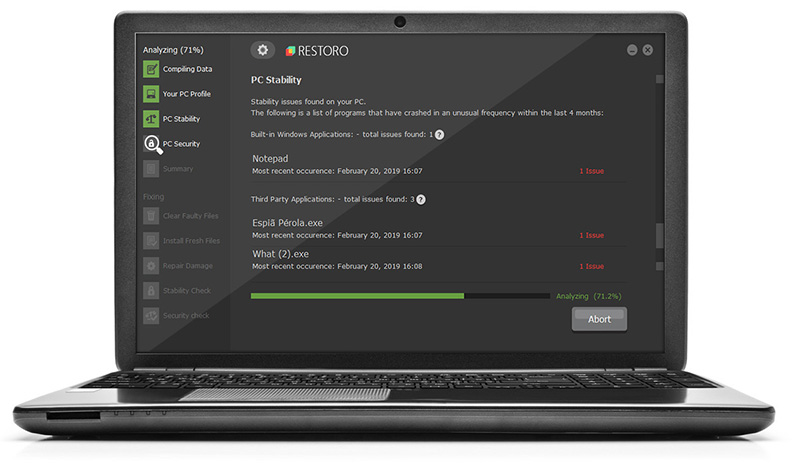
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.