What is Ims00ry ransomware? And how does it implement its attack?
Ims00ry ransomware is a dangerous crypto-virus that was discovered as of late. This new notorious ransomware infection does not add any extension to the files it encrypt although it includes the shlangan AES-256 file marker. It is designed to manipulate the legitimate look of specific files and infiltrates the system sneakily.
After it invades a computer, Ims00ry will begin to implement its attack starting with a data harvesting module that is classified into two main categories. The first one is responsible for extracting data from the computer that could reveal the identity of the users by scanning the system for strings like phone number, address, email address, real name, stored account credentials, and many more while the second one is the information about the computer’s hardware. After the first module implemented, it then employs the second module, stealth protection where it uses the harvested information along with some malicious components in order to bypass any security programs installed in the computer.
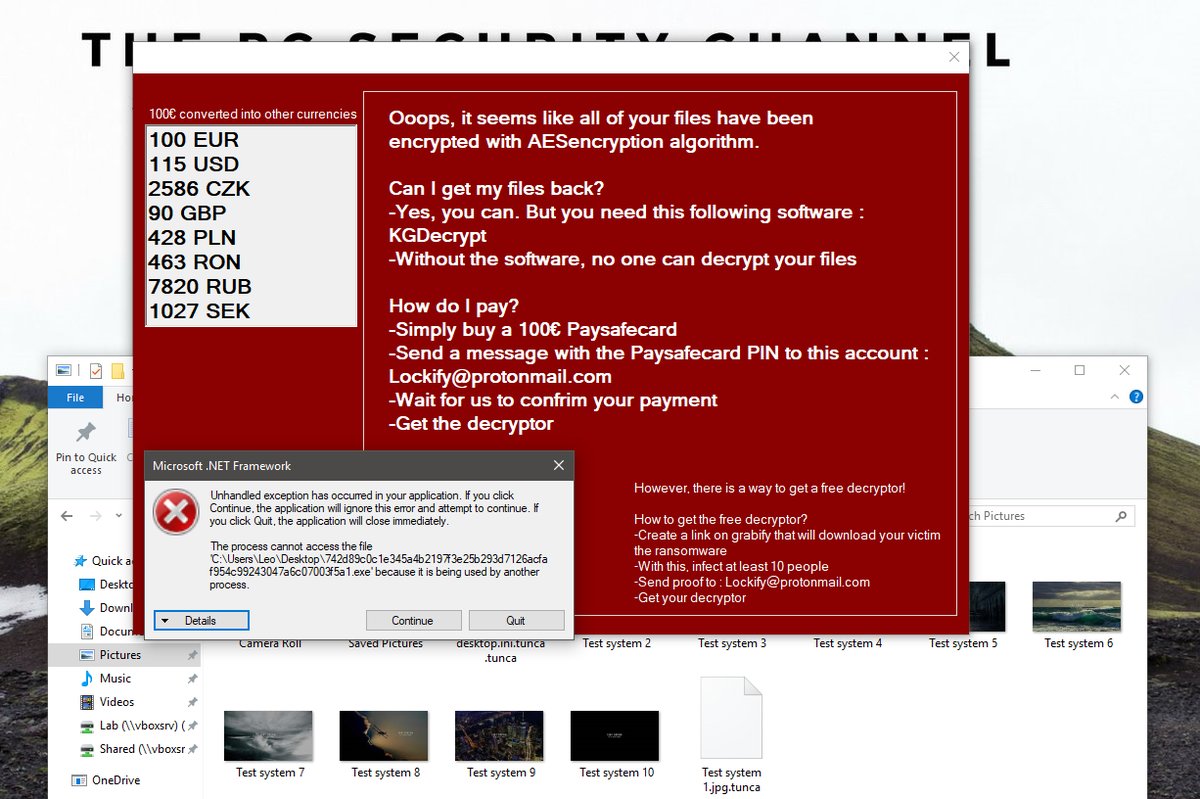
Moreover, Ims00ry ransomware also modifies the Windows Registry so that it can run automatically every time a user turns on the computer. It also scans the computer for its targeted files and starts the encryption using a combination of AES-256 and RSA-4096 encryption algorithms. Once the encryption process is completed, it changes the infected computer’s desktop wallpaper and opens a text file named “README.txt” which contains the following content:
“I am sorry !!!
My friend. I want to start my own business, but I have no money.
Your files is this photos the All, databases, and documents are encrypted by important OTHER with Strongest encryption algorithms and the RSA 4096, AES-256.
The
decrypt software is $ 50.
Attention !!!
Do not rename or move the encrypted files.
Bitcoin wallet:
1tnZbveCXmqRS1gfZSxztG5MbdJhptaqu
Contact Telegram bot:
@ lms00rybot”
If you are one of the victims of this ransomware threat, worry not for there is no need for you to purchase the decryptor used to restore compromised files since this file-encrypting malware’s code has been cracked and because of that, security experts from Emisoft were able to develop a free decryptor. But before you rush in recovering your encrypted files, you have to make the removal of Ims00ry ransomware from your system, your first priority. And besides the decryption software developed by security experts is free so there is no need for you to pay a cent.
How is the payload file of Ims00ry ransomware distributed online?
Like other ransomware threats, the malicious payload of Ims00ry ransomware may be disseminated through malicious spam email campaign. The authors of Ims00ry ransomware often attached seemingly safe files just like with the previous variant, the crooks added an attachment which they disguise as photos – and it may the same thing with the new variant although they might be using other file types such as documents or ZIP files so you have to be careful in downloading any email attachment no matter how harmless it may look.
To successfully wipe out Ims00ry ransomware from your infected computer, follow the removal guide laid out below as well as the advanced steps that comes next.
Step 1: First, boot your computer into Safe Mode with Networking and afterwards, you have to terminate the malicious processes of eCh0raix ransomware using the Task Manager and to open it, tap Ctrl + Shift + Esc keys.
Step 2: Go to the Processes tab and look for the malicious processes of eCh0raix ransomware and then right click on it and select End Process or End Task.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step 4: Look for dubious programs that might by related to eCh0raix ransomware and then Uninstall it/them.

Step 5: Close Control Panel and then tap Win + E to launch File Explorer.
Step 6: After opening File Explorer, navigate to the following directories below and look for eCh0raix ransomware’s malicious components such as a file named “README.txt” and a “[random].exe” file as well as other suspicious-looking files and then erase them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by eCh0raix ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by eCh0raix ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
After you’re done with the steps given above, you can recover your files by downloading this free decrypter from Emisoft. Once you’re done recovering your encrypted files, you need to continue the Ims00ry ransomware removal process using a reliable program like [product-name]. How? Follow the advanced removal steps below.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot it.
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.

- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.

- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.

- After the scan is completed click the “Fix, Clean & Optimize Now” button.